Ready to grab some important facts about the malicious floxif virus.
Awesome!
This article contains 7 ways of how to remove win32/floxif.e virus in Windows 10 OS.
Let's get started!!
Ready to grab some important facts about the malicious floxif virus.
Awesome!
This article contains 7 ways of how to remove win32/floxif.e virus in Windows 10 OS.
Let's get started!!
Share this article:
Share this article:
Floxif.e is a Windows executable file, which means that it is a malicious program capable of performing harmful activities on your computer when installed. Security experts have labeled this virus as a hazardous Trojan infection in the Trojans category.
When this dangerous malware enters your computer, it begins to execute malevolent activities in the background and wreaks havoc on the system. It places tracking cookies on all of your web browsers and maintains track of your online actions to collect information about your interests, demands, and other preferences.
The Win32/Floxif virus spreads via the third-party utility CCleaner executable, which hackers can exploit and inject a malicious payload.
After entry, the Floxif malware gathers a lot of information about the system (such as installed programs, unique ID numbers, MAC addresses, etc.) and transmits it to a control server.
Also, the harmful code is capable of recording your keystrokes and sending that data to cybercriminals.
When you log in to online forums, win32/floxif.e puts links in your posts that advertise dangerous things like illegal content or spam pages. When you click on these unauthorized ads, they may lead to sites with malicious software, which could infect your computer with even more severe computer diseases.
Win32/floxif.e virus should be removed immediately after discovery because it helps hackers steal essential information about you and your PC.
Suppose your system operates in a highly lagging manner. If websites open unusually, or you see ads at places they don’t belong, then it’s possible that a virus has infected and is now active on the computer.
The best way to remove the floxif virus is by using antivirus software like Malwarebytes, as it has been explicitly designed to detect and remove such threats from your system.
The main objective of Floxif Trojan is to steal vital information about you. The most recent versions are also detected by fake applications and other fraudulent names, such as the Trojan.Floxif.AppFish threat.
Win32/Floxif.e is a dangerous virus that installs unwanted software on your computer. This can be from adware and toolbars that slow down your Internet navigation to malware allowing hackers to access your system remotely.
How can Floxif Trojan get into your PC?
Floxif Trojan usually gets inside the computer system when you are not careful while installing software on your system. It also enters into it through fake links that come embedded in spam emails. Once it gets inside your computer, it changes the Windows registry and the Internet settings.
Floxif Trojan can hijack your web browsers and redirect your search results to unknown websites. The presence of this virus will also slow down your computer’s performance, as it uses a lot of CPU power.
The main task of Trojans is to steal information from unaware users and transmit it back to a third party, who then uses that sensitive data for illicit activities. Once inside, it will perform specific actions without the user’s consent or knowledge.
The first thing it does is drop the virus file in %System% like :
%Program Files\Common Files\system\symsrv.dll
%Program Files\Common Files\system\ffff.dll
Not restricted to this, it can further create these registry entries:
<p>HKLM\SOFTWARE\MICROSOFT\WINDOWSNT\CURRENTVERSION\WINDOWS|AppInit_DLLs</p>
<p>HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWSNT\CURRENTVERSION\WINDOWS|AppInit_DLLs</p>
It is recommended to use Malwarebytes specially designed to remove this harmful threat from the infected system. You can download Malwarebytes for free or purchase a licensed copy.
Malwarebytes is considered one of the recommended win32/floxif.h virus removal tool out there.
If the virus is still there, you can use Farbar Recovery Scan Tool (FRST) to gather logs and then send the two logs to the Malwarebytes support team for further study and assistance.
Follow these steps to download and run a scan on your system with Farbar Recovery Scan Tool (FRST):
Download the correct version of FRST for your operating system from here :
Only the suitable variant will operate on your system, while the other will display an error message. So, if you don’t know what version your computer is running, download both of them and select the one that works.
Step 1: After downloading, place the program (FRST.exe or FRST64.exe) on your Desktop.
Step 2: To launch the tool, double-click the file to run the tool.
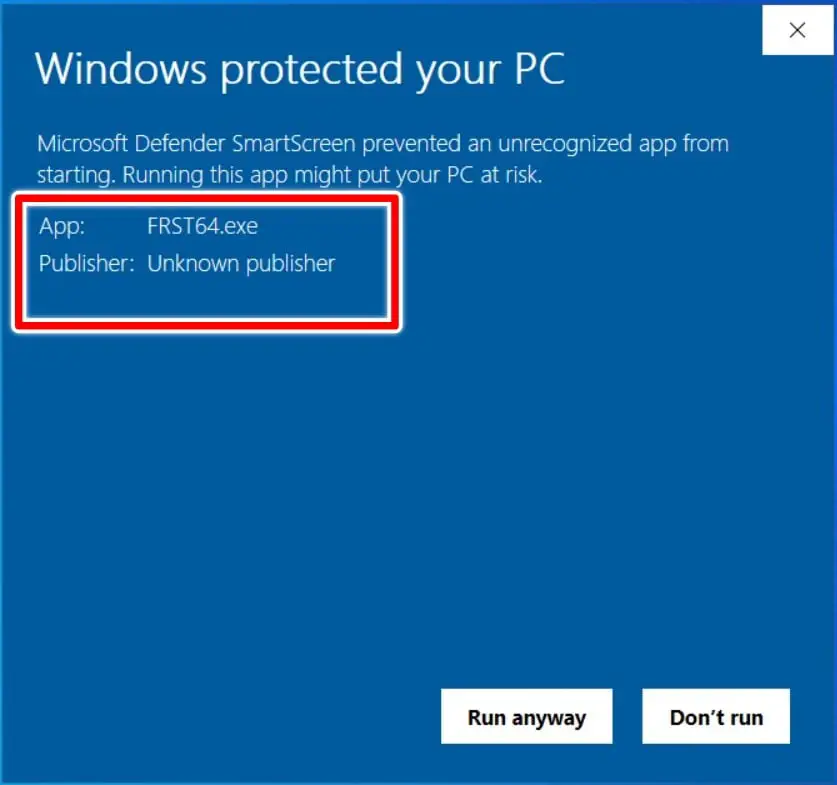
Step 3: It’s possible that a Windows secure notification will display. This alert is from the Windows Defender SmartScreen Filter, which stops unknown applications from running on your computer.

Step 4: Tap on More Info and click on Run anyway. More Info specifies the correct version of the executable.
Step 5: Tap on Yes on the next two subsequent windows – the User Access Control window & the disclaimer of warranty.
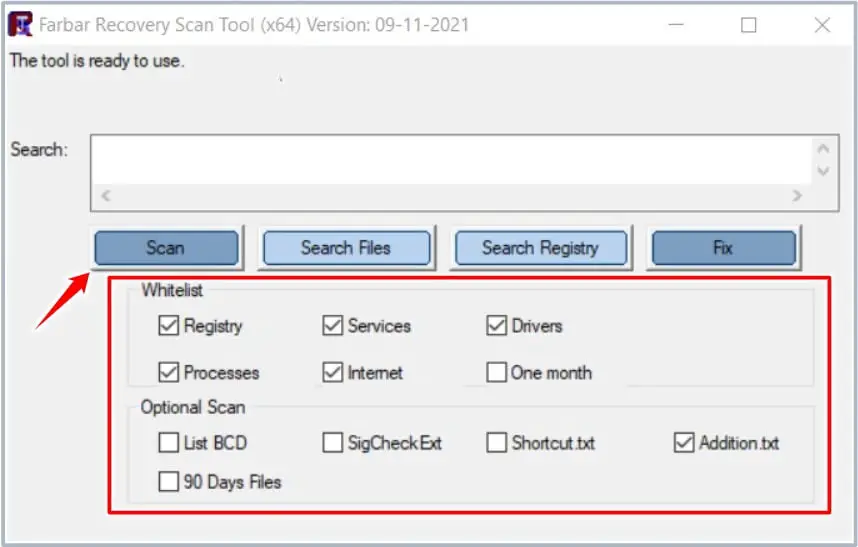
Step 6: Check the following boxes: Registry,Services,Drivers,Processes,Internet,Addition.txt
Step 7: Click the Scan button and wait for it to finish.
Step 8: The tool backs up the Registry before scanning your computer, taking a few seconds.
Step 9: When the scan is complete, two message boxes will open on which you need to tap on OK.
“Scan completed. FRST.txt is saved in the same directory FRST is located.”
“Addition.txt is saved in the same directory FRST is located.”
The entire content of both FRST.txt and Addition.txt files is to be sent over to the Malwarebytes support team for analysis.
Malicious programs may be pretty tenacious and may be tough to remove from your device. Microsoft Defender Offline can help you eliminate them using the most up-to-date threat definitions.
Windows Defender is completely free. Malwarebytes, on the other hand, offers a wide range of premium security software.
You can uninstall a PC program from your Windows 10 system by following these steps:

When deciding which application to remove, keep an eye out for applications that aren’t very recent. Viruses are frequently distributed with back dates.
Be careful when selecting everything around an application because if you accidentally deselect it, your PC could get stuck.
Much like defending against most typical cybersecurity threats, effective cybersecurity software should be your first line of defense. An effective internet security solution should run frequent scans and notify you when a Trojan virus is discovered.
Here are some of my recommendations to keep yourself safe online :
Buy Malwarebytes Now
Can Bluetooth be Hacked? Here are 11 Tips to be safe
Where is the Cheapest Place to Buy Stock Photos in 2021-2022?
What is a Gaming Monitor?—The Only Guide You Need in 2022!
Best DDR4 RAM for Gaming PCs in 2021
Unraveling the Magic of Artificial Intelligence: A Human Perspective
The Future of Artificial Intelligence: Unveiling Growth, Key Trends, and Evolution
Master syncing Xbox Companion App for an enhanced gaming experience.
Exploring the Basics of Game Mechanics Like Never Before